Pester 5.0 Released
Some sysadmins tinker with PowerShell scripts and write code that gets a task done. Other sysadmins write highly involved and complex scripts that are full of conditional testing. However, there is not really a lot of administrators that write their code with testing in mind. That is where Pester comes in.
I admit, I am not in the category of people that use Pester. But I should be. I have written very large scripts comprising of multiple module files. Pester will allow a sysadmin or syseng to make changes to the underlying code and if the pester file successfully processes then we know that any code changes did not break any functionality of the overall script.
With that said, check out the new release of Pester 5.0. https://github.com/pester/Pester/releases/tag/5.0.0
PowerShell 7 Release
With each new release of PowerShell, we get closer and closer to full compatibility with the legacy PowerShell. This is a very exciting release. The link below will take you to the Microsoft announcement release.
https://devblogs.microsoft.com/powershell/announcing-powershell-7-0/
A couple of the features that I think that have been long overdue are the foreach threading and the ternary operators. As someone who has been coding in C# for a long while, these have been fundamental language deficiencies.
For a full list of cmdlet implementation and compatibility, visit the following site: https://docs.microsoft.com/en-us/powershell/scripting/whats-new/cmdlet-versions?view=powershell-7

Going forward, PowerShell 7 will be the “one, true PowerShell” as well, supplanting the previous forked versions between Windows PowerShell and PowerShell Core.
PowerShell TLS 1.2 Only
Ever try to communicate with a remote API or URL only to receive an error message? Reviewing the code is usually the first step in troubleshooting.

However, as administrators in a large enterprise we have to understand the ever-growing changes in security framework requirements. SSL 3.0 and TLS 1.0 have already all become deprecated. TLS 1.1 will become end of life on March 31, 2020. This has triggered most enterprises to start disabling this functionality in their server infrastructure.
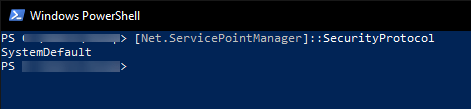
As an administrator, you can validate the security ciphers that PowerShell is currently utilizing with the following command
[Net.ServicePointManager]::SecurityProtocol
This will generate the following output.
To update the default communication cipher that PowerShell will utilize to communicate with a remote server, execute the following command:
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12